Join the Concordium Community, follow us on X.
While blockchain's radical transparency makes everyday business operations like payroll impossible, a new generation of privacy chains is solving this by balancing essential confidentiality with compliance-readiness.
Sarah runs payroll for a 50-person startup.
Every two weeks, she sends out $200,000 in salary payments. On Ethereum, that would mean:
- Junior developers instantly seeing the CTO earns 8 times more
- Competitors scraping transaction data to poach talent
- Vendors spotting a $2M treasury and raising prices overnight
- Every employee’s compensation turning into permanent public record
So Sarah sticks with traditional banking. Like almost every business does.
Because radical transparency doesn’t work for payroll, supplier payments, or corporate finance. It’s not how the real economy operates.
That’s the gap privacy chains are trying to close.
Modern privacy chains can hide sensitive details, amounts, recipients, balances, while still keeping transactions verifiable on-chain. In theory, Sarah could run payroll the same way she does through a bank: confidential by default, auditable when required.
But most privacy solutions break down in practice. They swing too far in one direction:
- Fully opaque systems trigger regulatory pushback
- Partial privacy systems fail to protect meaningful business data
The architectures that matter take a harder route: strong confidentiality paired with selective disclosure for compliance. This article explains how privacy chains work, why many approaches stall, and which designs may actually support mainstream adoption.
Key Takeaways
- Privacy chains protect transaction details and user data while maintaining network verifiability and integrity.
- Transparency builds trust in open systems, but it exposes sensitive financial activity in practical applications.
- Privacy is about normal business confidentiality, not concealing wrongdoing or illicit transactions.
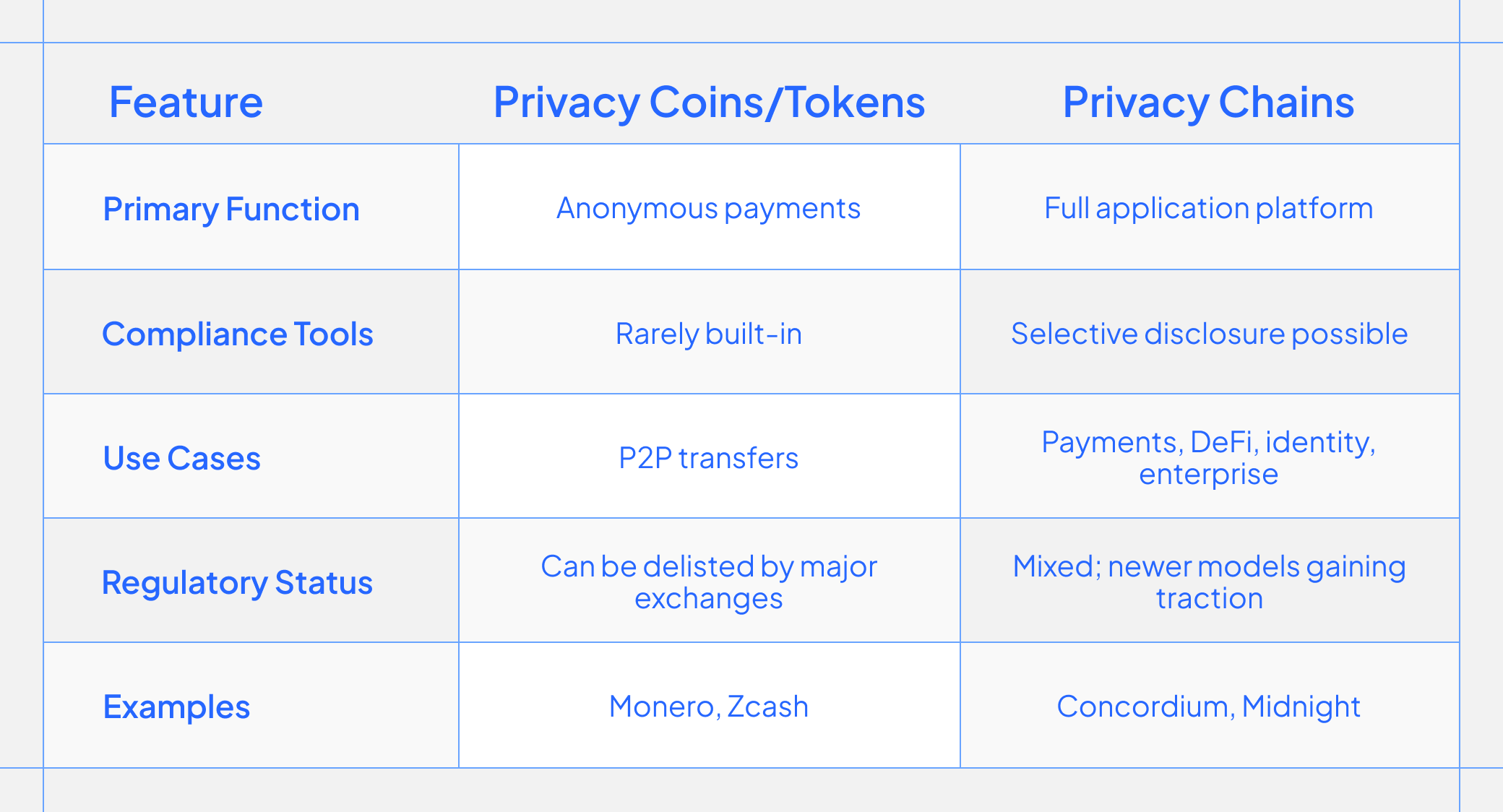
- Privacy coins focus on anonymous peer-to-peer transfers, while privacy chains support comprehensive programmable applications.
- The critical challenge is combining strong confidentiality with regulatory auditability and compliance mechanisms.
- Selective disclosure models enable controlled privacy that works for regulated institutions and enterprises.
- The future belongs to blockchains that successfully balance user privacy with institutional accountability requirements.
What Is a Privacy Chain, and How Does It Actually Work?
A privacy chain is a blockchain designed to protect sensitive information.
The goal is not to weaken verification, but to make confidentiality compatible with correctness. Privacy chains aim to deliver the benefits of blockchain (shared settlement, programmability, and trust minimization) without forcing users and businesses into radical transparency.
This requires a different technical foundation. Privacy chains often rely on zero-knowledge proofs to verify transactions without exposing details. These tools allow validators to confirm that a transaction is legitimate without learning what the transaction contains.
What Are Privacy Coins?
Privacy coins, sometimes also called privacy tokens, are cryptocurrencies designed specifically to participate in transactions that hide details, often prioritizing anonymity at the asset level. They live on a primitive privacy network, and are just one part of a larger infrastructure.
These systems typically focus on obscuring sender, recipient, or transaction amounts, enabling private transfers that cannot easily be traced. Technologies like ring signatures, stealth addresses, and coin mixing help break the link between transactions and identities.
“Exchanges have steadily delisted privacy coins as regulatory scrutiny has increased, shrinking their liquidity and institutional viability.” - Gate Research
Privacy tokens played an early role in demonstrating that confidentiality was possible on-chain. They proved that blockchain privacy was technically feasible and attracted users who valued financial discretion. However, many were designed primarily around anonymity rather than broader institutional or application needs.
The trade-off became clear over time. Strong anonymity that these coins contributed to made these systems difficult to integrate with regulated infrastructure. Exchanges delisted privacy coins under compliance pressure. Institutional adoption stalled because enterprises need auditability, not just secrecy.
Privacy Chains vs. Privacy Coins: More Than a Naming Difference
While privacy coins are used in anonymous payments and are just part of a bigger whole, newer privacy chains represent a broader evolution.
Privacy chains are programmable platforms supporting private applications, confidential smart contracts, selective identity proofs, and enterprise workflows. They extend privacy beyond simple value transfer into complex financial instruments, supply chain coordination, voting systems, and identity management.
A privacy token transfer hides who sent funds and how much. A privacy chain can execute a multi-party contract where each participant sees only their relevant information, validators confirm correctness without learning the details, and regulators can verify compliance through controlled disclosure mechanisms.
Some privacy chains emphasize flexibility: developers choose what stays hidden and what gets revealed.
The Cryptography Behind Privacy Chains: ZK Proofs, Encryption, and Confidential Computation
Zero-Knowledge Proofs
Zero-knowledge proofs allow one party to prove they know something or that a statement is true, without revealing the information itself. In the context of privacy chains, this means a user can prove their transaction is legitimate, that they have sufficient funds, that amounts balance correctly, that they're authorized to perform an action, without exposing transaction amounts, account balances, or counterparty identities.
Like proving you're over 21 without showing your ID, zero-knowledge proofs let you demonstrate facts without revealing data.
Encrypted Transactions
Privacy chains can encrypt transaction data so that amounts, sender addresses, and recipient addresses remain hidden from public view. The network still processes and validates these transactions, but the details remain confidential. Only authorized parties, those with the proper decryption keys, can see the specifics in some variants.
Encryption preserves the ability to compute on or verify the data while keeping it confidential. Validators confirm transactions follow the rules without decrypting the details.
Confidential Computation
Some privacy chains extend confidentiality beyond simple transfers into smart contract execution. Confidential computation allows contracts to process sensitive data without exposing that data to validators, other users, or even the contract deployer in some cases.
This enables private decentralized applications: lending protocols that don't reveal borrower positions, voting systems that hide individual votes while proving the tally is correct, or auctions where bids remain sealed until results are finalized. The computation happens on-chain and is verified by the network, but the inputs and intermediate states remain encrypted.
Privacy by Default vs. Selective Privacy: Two Very Different Promises
Not all privacy systems work the same way. The architectural choice between full anonymity and selective disclosure has major implications for adoption.
Privacy By Default (Full Anonymity)
Some privacy chains make everything private by default, with no mechanism to selectively reveal information. Every transaction is anonymous. No data can be disclosed, even under lawful conditions.
This approach maximizes confidentiality, but it creates problems for regulated use cases. If nothing can ever be revealed, institutions cannot audit, regulators cannot verify compliance, and enterprises cannot demonstrate adherence to legal requirements. Privacy-by-default systems often struggle to gain institutional adoption because they cannot bridge the gap between confidentiality and accountability.
Selective Privacy (Configurable Disclosure)
Newer privacy architectures allow users and developers to choose what remains hidden and what can be proven or revealed. Instead of making everything permanently anonymous, these systems support controlled disclosure mechanisms.
A user might prove they are not from a particular region without revealing their identity. A business might demonstrate tax compliance to an auditor without exposing all transaction details to the public. A lender might verify a borrower meets credit requirements without accessing their full financial history.
Selective privacy doesn't weaken confidentiality. It makes privacy compatible with real-world requirements. Users retain control over their data, but they can selectively prove things when necessary, for compliance, for business relationships, or for access to regulated services.
The Core Tension: Strong Privacy Chains Still Need an Accountability Layer
Early privacy systems were often optimized for secrecy above all else. But secrecy alone is not enough for global adoption.
Financial systems require auditability, rule enforcement, and lawful oversight. If activity cannot be assessed at all, institutions cannot participate, and regulators will treat the system as incompatible with compliance. Banks need to demonstrate adherence to anti-money laundering rules. Enterprises need auditable records for tax purposes. Exchanges need to verify that counterparties are not sanctioned entities.
“Major exchanges have removed Monero and similar assets to remain compliant with AML and KYC rules, forcing privacy projects to rethink their architectures around compliance.” – Cryptodamus
“Selective disclosure models are emerging as a standard way to reconcile confidential transactions with regulatory reporting and audit trails.” – Quantum Private
Why Regulators Challenge Most Privacy Chains
The issue is architectural. Privacy chains must provide confidentiality by default, but also allow accountability through due process when required.
Customer transactions are private from the public and from other customers, but banks can produce records during audits. Privacy exists within a framework of accountability. The same principle must apply to privacy chains if they want to operate within legal systems.
Many existing privacy protocols make this impossible. They provide strong anonymity but no pathway for authorized disclosure. This creates a binary choice for regulators: allow the system and lose oversight, or prohibit it entirely. Most choose prohibition.
Systems that cannot demonstrate compliance cannot gain institutional trust. Systems that cannot respond to lawful requests cannot operate in regulated economies. Privacy chains that want mainstream adoption must solve this problem, building architectures where privacy and accountability are both technically possible and legally enforceable.
Three Generations of Privacy Chains: How the Architecture Has Evolved
First Generation: Hiding Transactions, Nothing More
First-generation privacy chains focused mainly on hiding transaction details. They proved privacy was possible, but adoption remained limited outside niche communities. These systems prioritized anonymity over compatibility, making them difficult to integrate with regulated infrastructure. They served early adopters and ideological users, but struggled to gain traction with enterprises or institutions that needed auditability alongside confidentiality.
Examples: Zcash (shielded transactions), Monero (privacy-by-default transfers), Dash PrivateSend (early transaction mixing).
Second Generation: Privacy Moves Into Smart Contracts
Newer designs expanded privacy into smart contracts and application logic. This enabled broader use cases, but gaps remained around identity, compliance, and institutional trust.
Privacy 2.0 systems introduced programmable confidentiality, allowing developers to build private decentralized applications. Users could execute complex financial operations without exposing sensitive data, opening the door to private lending, trading, and asset management on-chain.
Examples: Secret Network (private smart contracts), Aztec (zk-based private execution on Ethereum), Oasis Network (confidential computation environments).
Privacy 3.0: Confidentiality That Can Coexist With Auditability
The latest evolution recognizes that privacy alone is not sufficient. Privacy 3.0 architectures combine confidentiality with selective disclosure mechanisms, allowing authorized parties to verify compliance without compromising user privacy. These systems support granular permission structures, cryptographic credentials, and auditable privacy where information can be proven without being revealed, or disclosed under specific legal conditions.
“Zero‑knowledge selective disclosure is already used in verifiable credential systems, where holders can prove specific attributes (like age) without revealing full IDs.” – IOTA
“Selective disclosure is the technical implementation of rational privacy. It gives users and developers the cryptographic tools to protect sensitive information by default, while still enabling the right level of transparency when it’s required.” – Midnight
Examples: Concordium (identity-backed selective disclosure), Midnight (programmable privacy with compliance support)
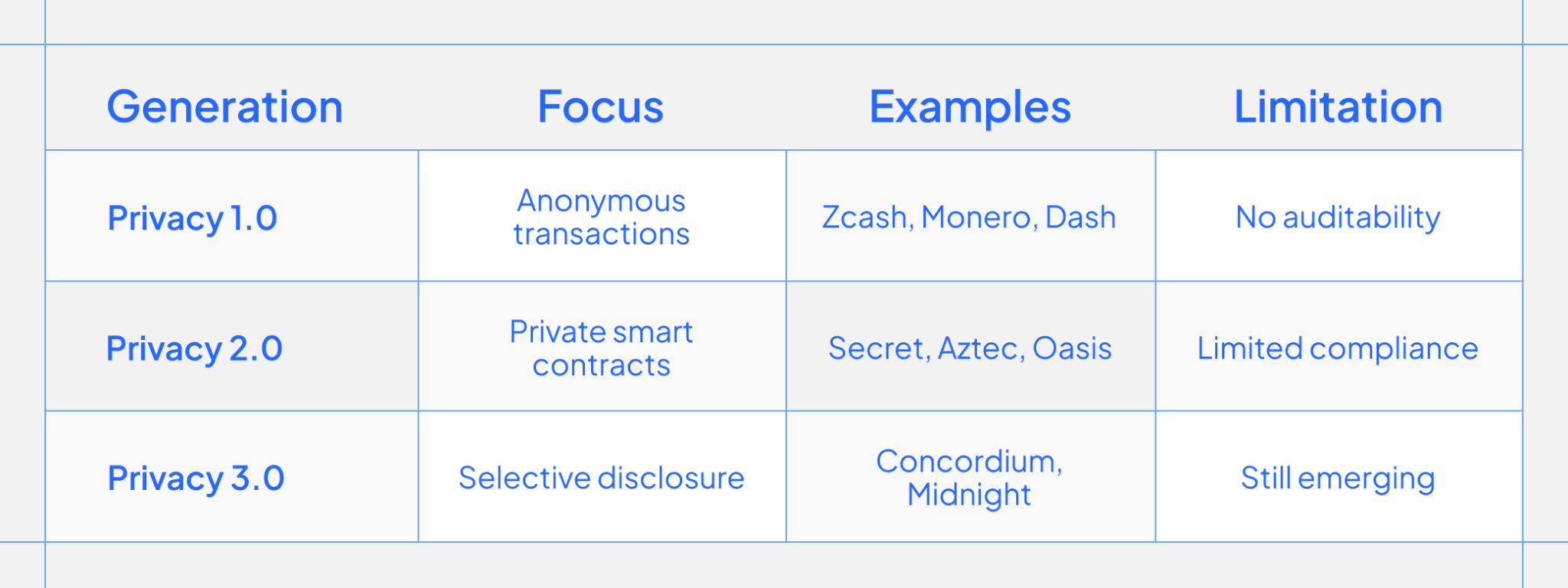
The evolution is clear: privacy alone is not sufficient. The next phase requires privacy that works within real economic and legal systems, balancing user confidentiality with institutional accountability in ways that make mainstream adoption possible.
How Concordium Approaches Privacy Differently
Concordium's approach is built around a key principle: privacy and accountability are not opposites.
Most privacy systems force a choice between confidentiality and compliance. Concordium rejects that framing. Instead, it treats privacy as the foundation and builds accountability mechanisms on top, creating a system where both can function without compromising the other.
Built-In Identity Without Public Exposure
Users can prove legitimacy or eligibility without exposing personal information on-chain. Identity becomes a tool for verification, not surveillance. Through zero-knowledge credentials, participants can demonstrate they meet requirements (age verification, accreditation status, jurisdictional eligibility) without revealing who they are or linking their on-chain activity to their real-world identity.
This changes the economics of privacy. Traditional systems either expose everything or hide everything. Concordium allows selective proof. A user can show they are not a sanctioned entity without disclosing their name. They can prove they hold a credential without revealing other attributes. Identity exists in the system, but it remains private unless there is a legitimate reason to disclose it.
Privacy With Lawful Disclosure
Accountability is enabled only under strict legal processes. Privacy remains the default, while disclosure is the exception. Concordium incorporates anonymity revokers, entities that can decrypt user identities only when presented with valid legal authority. Disclosure is only possible under defined legal process through anonymity revokers (also known as Privacy Guardians) and Identity Providers (IDPs).
Disclosure requires due process, it cannot happen arbitrarily. The system enforces privacy cryptographically while maintaining the technical capacity for lawful oversight when justified. This makes Concordium compatible with auditability requirements without sacrificing user confidentiality in normal operation.
Why This Works
This architecture supports real-world adoption: regulated payments, enterprise workflows, consumer markets, and compliance-ready finance. Businesses can transact privately while meeting auditability requirements. Users can operate confidentially while institutions verify they are not violating rules. Regulators can enforce laws without demanding universal surveillance.
The result is a privacy chain that does not require choosing between user rights and institutional trust. It provides both, structurally, making it viable for use cases that existing privacy systems cannot serve.
Real-World Use Cases
Current privacy chains can unlock adoption in areas where transparency fails. They can represent the core functions of any working economy, currently impossible on public blockchains without privacy infrastructure.
Payments: Salaries, Subscriptions, Retail Purchases
This is our example from the introduction. No employee wants their salary visible to coworkers or the public. No consumer wants their spending history permanently broadcast. Privacy chains can make routine payments feasible on-chain by hiding amounts and counterparties while preserving settlement guarantees. Payroll systems can operate without exposing compensation. Subscription services can charge users without creating a public record of their preferences.
Identity: Proving Age or Eligibility Without Sharing Full IDs
Privacy chains enable selective disclosure of credentials. A user can prove they are over 18 without revealing their birthdate. They can demonstrate accredited investor status without exposing their net worth. They can show residency in a permitted jurisdiction without disclosing their address. This makes compliance possible without surveillance.
Enterprise: Treasury Operations and Supplier Confidentiality
Businesses cannot function if competitors can monitor their cash positions and payment relationships. Privacy chains allow companies to manage treasuries on-chain, pay suppliers, and execute contracts without exposing commercial strategy. Procurement remains confidential. Negotiated pricing stays private. Operational data does not leak to rivals.
Sensitive Platforms: Regulated Access Without Data Hoarding
Services that require age verification, geographic restrictions, or credential checks can enforce rules without collecting personal information. Users prove eligibility cryptographically. Platforms verify compliance without storing sensitive data. This reduces liability and eliminates honeypots of exploitable information.
Institutional Finance: Privacy With Auditability
Banks, asset managers, and trading firms need confidentiality for competitive reasons and auditability for regulatory ones. Privacy chains that support selective disclosure allow institutions to operate privately while demonstrating compliance to authorized auditors. This bridges the gap between blockchain transparency and institutional requirements.
Privacy chains serve everyone who needs confidentiality as a basic condition of participation.
How To Evaluate a Privacy Chain
What exactly is private: transactions, contracts, identity?
Not all privacy is equal. Some chains hide transaction amounts but expose participants. Others obscure sender and receiver but reveal smart contract logic. Understand what remains confidential and what stays visible. Comprehensive privacy should extend across transactions, contract execution, and user identity without forcing trade-offs between them.
Is selective disclosure possible?
Systems that hide everything permanently cannot serve regulated use cases. Look for mechanisms that allow users to prove compliance, share information with auditors, or respond to lawful requests without exposing their entire transaction history. Selective disclosure is what separates privacy infrastructure from anonymity tools.
Can institutions audit under lawful conditions?
Real-world adoption depends on institutional participation. Enterprises need audit trails. Regulators need verification pathways. Chains that provide no mechanism for authorized oversight will remain isolated from mainstream finance, regardless of technical quality.
Is it designed for long-term regulatory viability?
Privacy systems built around absolute anonymity face existential regulatory risk. Chains designed with compliance mechanisms embedded from the start have a path to legitimacy. Evaluate whether the architecture anticipates legal requirements or ignores them.
Privacy is only useful if it can scale into real markets. The right evaluation framework separates systems built for ideological purity from those built for practical adoption.
What Privacy Chains Need to Become to Win Mainstream Adoption
The infrastructure that wins will not be the most anonymous or the most transparent. It will be the systems that recognize privacy and oversight as complementary requirements, not competing values. Financial institutions, enterprises, and everyday users all need confidentiality. Regulators, auditors, and legal systems all need verification pathways. Both demands are legitimate.
The next era will be defined by systems that combine confidentiality with trust, auditability, and lawful oversight. These platforms will support private payments at scale, confidential enterprise operations, and regulated markets simultaneously. They will use cryptography not just to hide information, but to prove compliance without exposure.
The future belongs to chains that solve the hard problem: making privacy compatible with the legal, economic, and institutional frameworks that govern modern finance.
Join the Concordium Community, follow us on X.
FAQ
Are privacy chains slower than regular blockchains?
It depends on the technique. Zero-knowledge proofs add computational overhead, making some privacy chains slower than transparent ones. However, newer architectures optimize performance, Concordium, for example, maintains speeds comparable to standard proof-of-stake chains while adding privacy.
Are privacy chains legal and compliant with regulations?
Privacy chains face regulatory scrutiny when they offer no mechanism for lawful verification or auditing, making them incompatible with regulated markets. However, newer privacy architectures that support selective disclosure and controlled accountability under legal processes can operate within regulatory frameworks, balancing user confidentiality with institutional compliance requirements.
Can privacy chains support businesses and institutions?
Yes, privacy chains enable enterprises to manage treasury operations, pay suppliers, and execute contracts without exposing commercial strategy to competitors while still meeting audit requirements. Systems designed with selective disclosure allow businesses to operate privately while demonstrating regulatory compliance to authorized auditors when required.
How can privacy exist without enabling misuse?
Privacy systems can incorporate controlled disclosure mechanisms that maintain confidentiality by default but allow authorized parties to verify compliance under strict legal processes. This architectural approach uses cryptography to prove legitimacy without exposing details, and provides lawful oversight pathways without requiring universal surveillance or eliminating user privacy.
What makes a privacy chain suitable for real-world adoption?
A privacy chain becomes suitable for real-world use when it combines strong confidentiality with selective disclosure mechanisms, supports both user privacy and institutional auditability, and can operate within legal frameworks without forcing a choice between compliance and protection. Real-world viability requires privacy that works for regulated payments, enterprise workflows, and consumer markets simultaneously.
How does Concordium balance privacy and accountability?
Concordium uses built-in identity systems that allow users to prove eligibility or legitimacy without exposing personal information on-chain, treating identity as a verification tool rather than surveillance. The platform incorporates controlled disclosure mechanisms that maintain privacy as the default but enable accountability only under strict legal processes, creating a system where confidentiality and compliance coexist structurally rather than competing.


